Here’s one I learned by starting with Jason Skinner videos on YouTube, but also by listening to the original from Don Reno over and over. I’ll never play it as well as he did, but at least I got to play on his banjo once.
Let me know what you think!
This too shall pass.
Here’s one I learned by starting with Jason Skinner videos on YouTube, but also by listening to the original from Don Reno over and over. I’ll never play it as well as he did, but at least I got to play on his banjo once.
Let me know what you think!
During this insane quarantine time we are all stuck in the middle of, I started working on a new album that, unlike my last one, won’t be in the electronica realm. Now that I’ve finally built somewhat of a home studio where I can play instruments and be loud without the need to channel everything through headphones, my options are much more inspiring.
That, coupled with this deep, intense angst that many of us are feeling as we are trapped at home under this new but hopefully temporary way of living, led to the following track that I hope you enjoy.
It is available on iTunes, Spotify, Amazon, and all the usual places, but you can also listen to it here:

We played our second show recently, and the good George Hodges produced a fine live recording of it for everyone to hear.
The Internet Archive, the same people who bring you the Wayback Machine, is a great place where live music recording enthusiasts are posting all kinds of great stuff for free listening. Not only is the Ska City show there, but there are millions of other things you can get lost in listening to as well.
Here’s the Ska City show:
https://archive.org/details/SC2019-12-11.m1280.24
And here’s the page you can start on to choose your own musical adventure:
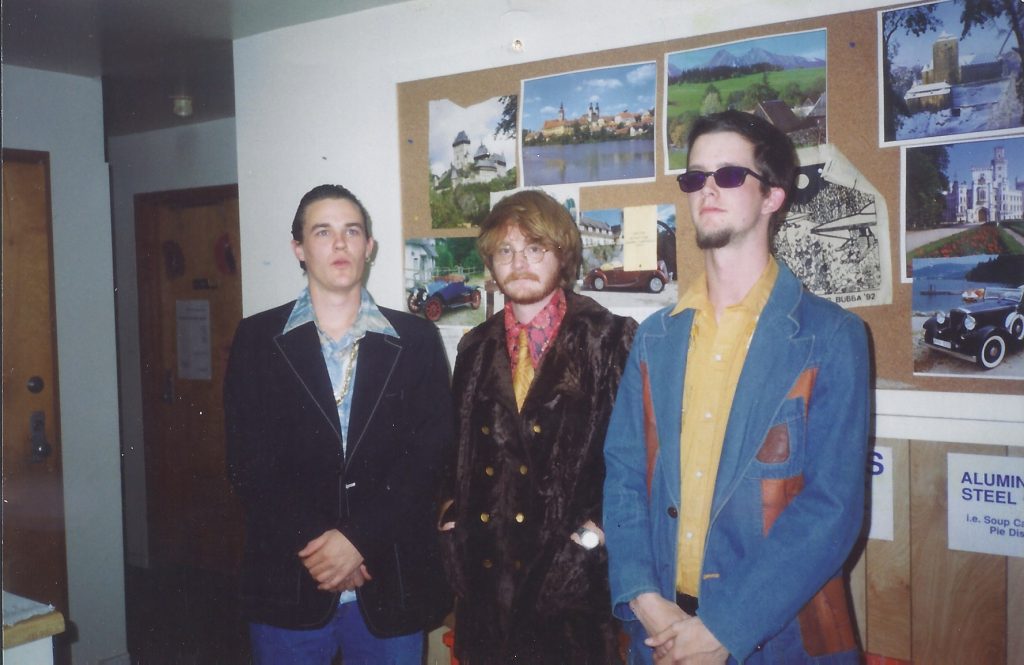
Way back in the good years of 1992-1993 or so I was in a band called Merle, based at Warren Wilson College. As a three-piece, we produced some insane sounds, surrounded ourselves with more insane antics, and had a hell of a time doing it.
Merle went on to become The Merle when Morgan Geer joined the band, and our notoriety in Asheville and beyond started to grow. Eventually, I left the band (I was the only one still in school at that point), but The Merle continued on and became an Asheville legend.
An old pal from Warren Wilson (Richard Stowe) recently dug up a tape of a live recordings and some demos that Merle had done from 1992 or 1993. Another old pal (George Hodges) cleaned up the tape, remastered it, and put it out there for you all to enjoy!
Beware: there are vulgarities at certain points, where we asked friends to join us on stage.
The most striking (you locksmiths will get that joke) thing about this is that an expensive “smart” lock was made with little to no physical security features in mind. I like how the article points out the difficulty of physically compromising a good-ole-fashioned steel, “dumb” mortise lock.
Is it true that “smart” lock manufacturers are forgetting about physical security when designing locks? Isn’t that the point of a lock?


In recent weeks I have been reading comments online about the Penetration Testing with Kali Linux (PWK) course and OSCP exam taking a lot of flak for being “tool old” and using “outdated exploits that don’t even work anymore.”
I believe most of these comments are directed at the lab environment and course materials. It is true that you won’t find many systems in modern pentesting engagements that are exploitable with older things such as EternalBlue (MS17-010).
But that is beside the point.
The PWK and OSCP exam are all about teaching you how to think, solve problems, persevere, and develop a pentesting methodology that works for you.
It is true that Hack The Box (HTB) and other modern online capture-the-flag frameworks are more leading-edge in that regard, which is great, and they can certainly be an excellent way to augment and prepare for the PWK/OSCP journey.
But the point is that it really doesn’t matter if you drive a 2019 Ferrari 488 Spider or a 1996 Honda Accord, it is whether or not you figure out how to get to the destination.
It’s been a while since I posted any musical updates here, and I don’t have a ton to share, but I did get a surprise email from the venerable Jason Lowenstein the other day, with a remastered set of Crain’s studio appearance on WMBR in Boston back in 1991 that he had made.
The previous version of this, mastered by Bob Weston, who initially recorded it in the studio late that evening way back when, is still here on my Music downloads page, and it is great, but I thought I’d add Jason’s version for you to download in one fell swoop.
Enjoy it, and let me know what you think!

As you may or may not know, I was a locksmith for the better part of a decade, working on campus at Warren Wilson College as a student, learning the trade as I earned my BA in psychology, then being hired to work there and train other students after I graduated for about 4 years. I also ran my own business (Chatham’s Lock & Key) for about two years, and I did a stint at Willis Klein up in Louisville for a summer.
So it was interesting to me that once I started attending information security conferences, I saw how popular lock picking has become among that otherwise computer-based hacking crowd. They have “lock picking villages” where you can learn to pick locks, contests to pit your skills against others, and there are now loads of videos and tutorials online for “locksport” enthusiasts.
I was resistant to get into “locksport” for a while, perhaps because I had “been there, done that,” but also because the phrase “locksport” annoyed me.
However, I lost that battle when I found my old lock pick set from back in the day, and then found myself working a Master lock I had in the garage. Check out my first contribution to the Locksport community in this video.
Stay tuned for more.
When I did a short work stint at Secure Decisions in 2018, one of the projects I got to work on was helping to create the Attack Surface Detector plugin for ZAP and Burp Suite. I left that position before the project got published, but I am happy to see that it was a success.
From the OWASP description:
The Attack Surface Detector tool uncovers the endpoints of a web application, the parameters these endpoints accept, and the data type of those parameters. This includes the unlinked endpoints a spider won’t find in client-side code, or optional parameters totally unused in client-side code. It also has the capability to calculate the changes in attack surface between two versions of an application.
There is a video that demonstrates the plugin, and yes, that is me doing the voice-over.
Since recently discovering there is now an official Kali Linux docker image, I’ve been fiddling with it and tweaking my own setup to get it to how I like it for the things I use it for. I have a work version and a personal version. What follows is my personal version, used mostly for R&D, CTF challenges, and bug hunting in my free time.
# The Kali linux base imageFROM kalilinux/kali-linux-docker# Update all the things, then install my personal favesRUN apt-get update && apt-get upgrade -y && apt-get dist-upgrade -y && apt-get install -y \ cadaver \ dirb \ exploitdb \ exploitdb-bin-sploits \ git \ gdb \ gobuster \ hashcat \ hydra \ man-db \ medusa \ minicom \ nasm \ nikto \ nmap \ sqlmap \ sslscan \ webshells \ wpscan \ wordlists # Create known_hosts for git cloning things I wantRUN mkdir /root/.sshRUN touch /root/.ssh/known_hosts# Add host keysRUN ssh-keyscan bitbucket.org >> /root/.ssh/known_hostsRUN ssh-keyscan github.com >> /root/.ssh/known_hosts# Clone git reposRUN git clone https://github.com/danielmiessler/SecLists.git /opt/seclistsRUN git clone https://github.com/PowerShellMafia/PowerSploit.git /opt/powersploitRUN git clone https://github.com/hashcat/hashcat /opt/hashcatRUN git clone https://github.com/rebootuser/LinEnum /opt/linenumRUN git clone https://github.com/maurosoria/dirsearch /opt/dirsearchRUN git clone https://github.com/sdushantha/sherlock.git /opt/sherlock# Other installs of things I needRUN apt-get install -y \ python-pipRUN pip install pwntools# Update ENVENV PATH=$PATH:/opt/powersploitENV PATH=$PATH:/opt/hashcatENV PATH=$PATH:/opt/dirsearchENV PATH=$PATH:/opt/sherlock# Set entrypoint and working directory (Mac specific)WORKDIR /Users/wchatham/kali/# Expose ports 80 and 443EXPOSE 80/tcp 443/tcpdocker build -t yourname/imagename path/to/theDockerfile (don’t actually put ‘Dockerfile’ in the path). Do change ‘imagename’ to something apropos, such as ‘kali’
docker run -ti -p 80:80 -p 443:443 -v /Users/yourname/Desktop:/root yourname/imagenameThe above examples require you to replace ‘yourname’ with your Mac username
-ti
Indicates that we want a tty and to keep STDIN open for interactive processes
-p
Expose the listed ports
-v
Mount the defined folders to be shared from host to docker.
Hope that’s useful to someone!
Hat tip: https://www.pentestpartners.com/security-blog/docker-for-hackers-a-pen-testers-guide/